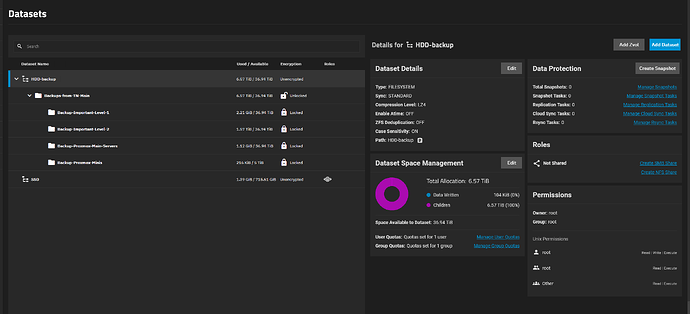
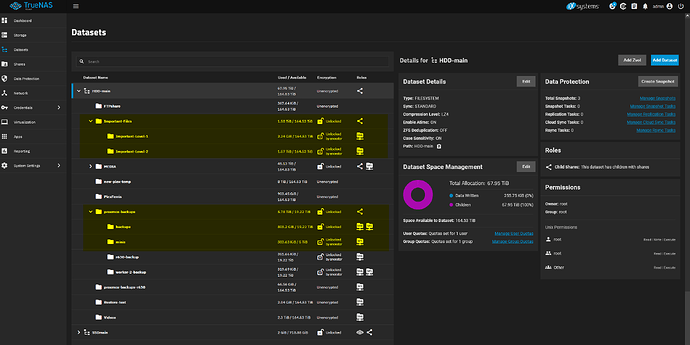
For the first time, I’m running a backup instance of TrueNAS and am pulling from my main to backup. Both are running Scale Dragonfish. I have no idea why this is happening, but 1. I can’t create a dataset that is an encrypted root dataset, so I have to nest datasets, and 2. the nested dataset will show unlocked until I do my first pull. At that time, the dataset becomes locked on it’s own, and no key that I have will unlock the dataset. Any ideas why it’s locking by itself, or how to unlock the dataset? Seems like a waste of a Truenas if pulling locks the data in a way you can’t access it, should the main TN break.
Pulling / replication from my main TN to my backup TN locks the dataset on the backup w/ unknown key
Trying to understand what you’re doing.
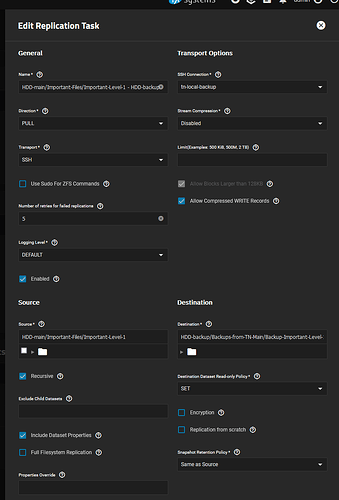
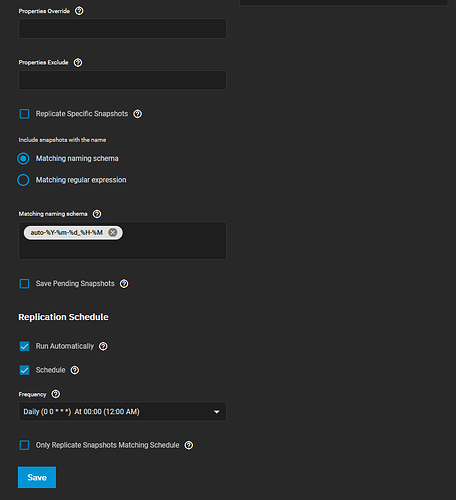
How is the Replication Task configured? Don’t just summarize it. Show every option, even if they seem unimportant.
What is the state of encryption on your source and destination datasets?
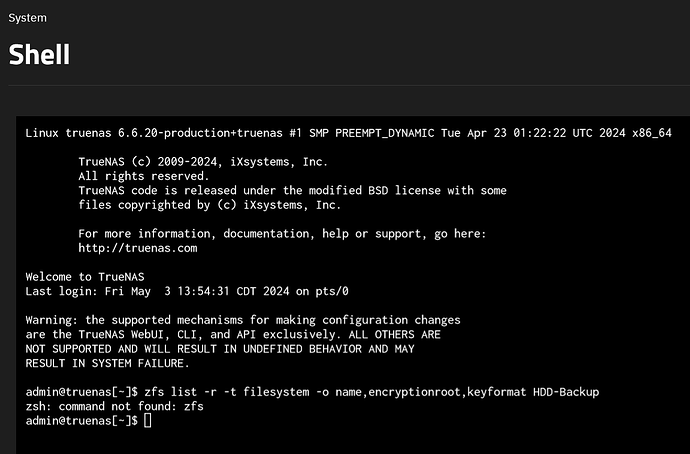
zfs list -r -t filesystem -o name,encryptionroot,keyformat <poolname>
zfs command not found?
Did you change your user’s $SHELL?
I’m not sure what the default is for SCALE.
I think I know what’s going on, but need to check one more thing: What about the results of that command for your source pool as well?
Are you able to paste the output in codeblock text format? Screenshots of text are discouraged for forums.
sorry about that.
Here’s the output from the source machine. very weird.
admin@truenas:~$ sudo zfs list -r -t filesystem -o name,encryptionroot,keyformat HDD-main
[sudo] password for admin:
Sorry, user admin is not allowed to execute ‘/sbin/zfs list -r -t filesystem -o name,encryptionroot,keyformat HDD-main’ as root on truenas.local.
I will say this data on the source was copied from another Truenas recently for me by a friend. I’m not sure what method he used to accomplish this.
Can you try it again without sudo?
I take it admin was given sudo privileges?
hmm for some reason admin didn’t have sudo privileges enabled.
Here’s the new output
admin@truenas:~$ sudo zfs list -r -t filesystem -o name,encryptionroot,keyformat HDD-main
[sudo] password for admin:
NAME ENCROOT KEYFORMAT
HDD-main - none
HDD-main/FTPshare - none
HDD-main/Important-Files HDD-main/Important-Files hex
HDD-main/Important-Files/Important-Level-1 HDD-main/Important-Files hex
HDD-main/Important-Files/Important-Level-2 HDD-main/Important-Files hex
HDD-main/MEDIA HDD-main/MEDIA hex
HDD-main/MEDIA/Movies HDD-main/MEDIA/Movies hex
HDD-main/MEDIA/TV HDD-main/MEDIA/TV hex
HDD-main/MEDIA/completed-dl HDD-main/MEDIA/completed-dl hex
HDD-main/MEDIA/completed-dl/manual HDD-main/MEDIA/completed-dl/manual hex
HDD-main/MEDIA/completed-dl/reading HDD-main/MEDIA/completed-dl/reading hex
HDD-main/MEDIA/completed-downloads HDD-main/MEDIA/completed-downloads hex
HDD-main/MEDIA/reading HDD-main/MEDIA/reading hex
HDD-main/MEDIA/yt-downloads HDD-main/MEDIA/yt-downloads hex
HDD-main/PlexFerris - none
HDD-main/Restore-test - none
HDD-main/Videos - none
HDD-main/new-plex-temp - none
HDD-main/proxmox-backups HDD-main/proxmox-backups hex
HDD-main/proxmox-backups-r630 - none
HDD-main/proxmox-backups/backups HDD-main/proxmox-backups/backups hex
HDD-main/proxmox-backups/minis HDD-main/proxmox-backups hex
HDD-main/proxmox-backups/r630-backup HDD-main/proxmox-backups hex
HDD-main/proxmox-backups/worker-2-backup HDD-main/proxmox-backups hex
sorry this really doesn’t format well when cut and pasted as text.
admin@truenas:~$ sudo zfs list -r -t filesystem -o name,encryptionroot,keyformat HDD-main
[sudo] password for admin:
NAME ENCROOT KEYFORMAT
HDD-main - none
HDD-main/FTPshare - none
HDD-main/Important-Files HDD-main/Important-Files hex
HDD-main/Important-Files/Important-Level-1 HDD-main/Important-Files hex
HDD-main/Important-Files/Important-Level-2 HDD-main/Important-Files hex
HDD-main/MEDIA HDD-main/MEDIA hex
HDD-main/MEDIA/Movies HDD-main/MEDIA/Movies hex
HDD-main/MEDIA/TV HDD-main/MEDIA/TV hex
HDD-main/MEDIA/completed-dl HDD-main/MEDIA/completed-dl hex
HDD-main/MEDIA/completed-dl/manual HDD-main/MEDIA/completed-dl/manual hex
HDD-main/MEDIA/completed-dl/reading HDD-main/MEDIA/completed-dl/reading hex
HDD-main/MEDIA/completed-downloads HDD-main/MEDIA/completed-downloads hex
HDD-main/MEDIA/reading HDD-main/MEDIA/reading hex
HDD-main/MEDIA/yt-downloads HDD-main/MEDIA/yt-downloads hex
HDD-main/PlexFerris - none
HDD-main/Restore-test - none
HDD-main/Videos - none
HDD-main/new-plex-temp - none
HDD-main/proxmox-backups HDD-main/proxmox-backups hex
HDD-main/proxmox-backups-r630 - none
HDD-main/proxmox-backups/backups HDD-main/proxmox-backups/backups hex
HDD-main/proxmox-backups/minis HDD-main/proxmox-backups hex
HDD-main/proxmox-backups/r630-backup HDD-main/proxmox-backups hex
HDD-main/proxmox-backups/worker-2-backup HDD-main/proxmox-backups hex
hopefully that’s better
if there’s a better way to format this that you are looking for, let me know.
It looks like the way you configured (and executed) your Replication Tasks have cleaved dependent datasets from their original “encryptionroot”. (This isn’t really a problem, since all that does it make these backup datasets their own independent encryptionroots.)
You need to open up your main pool’s “keys” file in a text editor. (It’s the file that ends with the .json extension.)
Within, you will find the relevant HEX strings, which you can copy+paste to manually unlock the backup datasets. After you unlock all of them, then you can export a working “keys” file (.json) for the “HDD-backup” pool.
Just be very careful going forward. The more complex your dataset layout becomes, the greater the risk of making a mistake in terms of backing up your “keys” for the encrypted datasets.
Rule of thumb: Have ALL datasets unlocked for a pool, and export the “keys” file. Do this for EVERY pool. And make sure they are kept somewhere secure and safe. Also make sure to export your config file with the secret seed.
Make this a routine practice.
hey, I’ve been in the hospital with pneumonia, but I just wanted to come back and say this worked. thank you.
Hope you’re better now! ![]()
Thank you!